Meet and exceed data privacy requirements
Encryption to ensure nobody can see your data
Data encryption is a security technique that translates data into encrypted form to make raw data invisible and prevent unauthorized access . Encryption keys are needed to decrypt the data, making it useless without them.
Data encryption is a security method where data is translated from plaintext to ciphertext (encrypted data), so that no one can see the original data anymore. This ensures that data is secure, even in extreme cases when an attacker gains operating system or database admin privileges or even steals the storage media/hardware entirely. Anyone who wants to see the original data needs to decrypt the data with the decryption key first. Without the decryption key, encrypted data is useless.
PlanItSecure’s data privacy infrastructure integrates with external key vaults to retrieve the key to be used in encryption/decryption. This gives the data owner full control over the encryption key and eliminates the need to trust anyone else for data security, even if the underlying infrastructure is entirely managed by another party, as in cloud IaaS (e.g. AWS, Azure) or PaaS (Platform-as-a-Service) deployments.
Search Booster to unlock the business value of data
Encryption is great for data security but it can hinder searching through encrypted data, as each record must be decrypted and checked to see if it's a match.
Encryption is great to eliminate the need to trust others. It is like locking the data and being confident that no one else can access it anymore. It comes with a downside though. When you run a search over encrypted data, first you need to decrypt the record, and check to see if it’s match. And you must do it for all the records. So, a typical search through encrypted data is like searching for something in a dark room, where you need to touch and hold every single item, one by one, until you find what you are looking for.
PlanItSecure provides Search Booster features and enables you to run fast searches and complex data queries, which helps you continue to use personal data as dynamically as before without locking the business value of data.
Eliminate excessive privileges over personal data
Excessive privilege in organizations can lead to errors when users have access to data they shouldn't, especially if that account is known to a disgruntled former employee or compromised by an attacker.
Excessive privilege exists in most organizations and errors are likely to occur when users can see data they shouldn’t be able to. Especially if that over-privileged account is known to a disgruntled former employee, or if an attacker gains control over it.
PlanItSecure granularly manages who can see what data. Custom tags, user consents, and data masking features can be used as on-the-fly filters to limit users from seeing certain records, certain fields of those records, and even certain parts of those data fields. This ensures only the required piece of data is visible in order to fulfill the job-related tasks, and privileges are always in accordance with data privacy regulations.
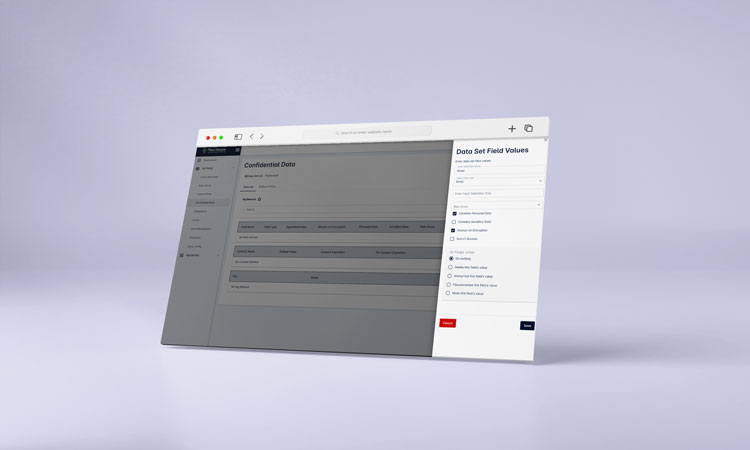
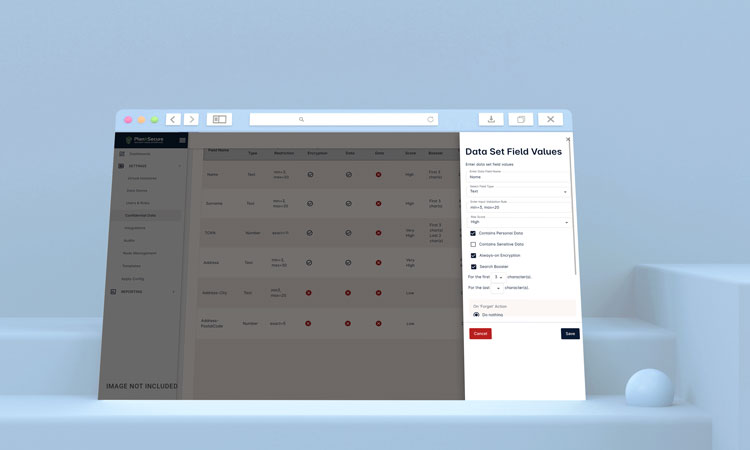
Data Classification to categorize personal and sensitive data
The more you know your data, the more tightly you protect it and comply with legal regulations.
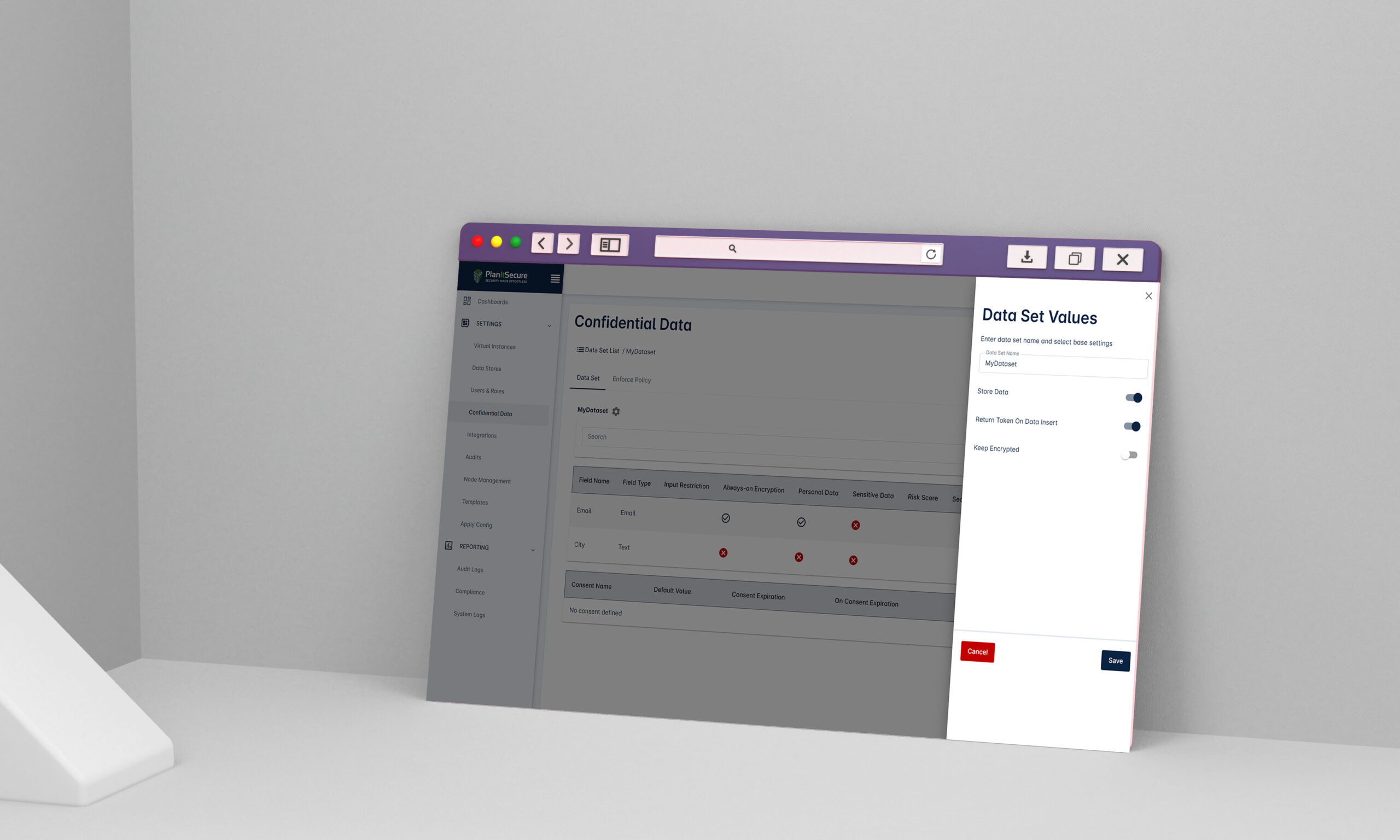
Security starts with knowing what you have. Data classification consists of organizing data into categories that make it easy to retrieve, store, and secure. It helps to determine data governance rules, protection techniques to be used, and simplifies regulatory compliance.
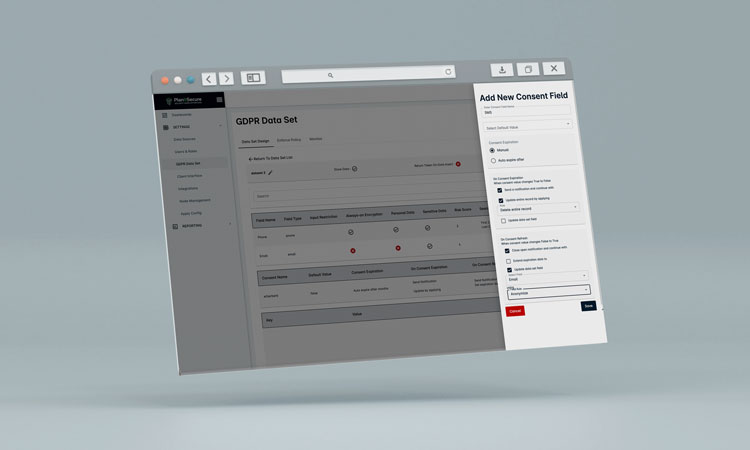
PlanItSecure provides a powerful and easy-to-use data definition interface where data owners can define their data fields, categorize the ones containing personal or sensitive data, and ensure the integrity and accuracy of their data. It also allows the use of custom tags like confidential, restricted, and public.
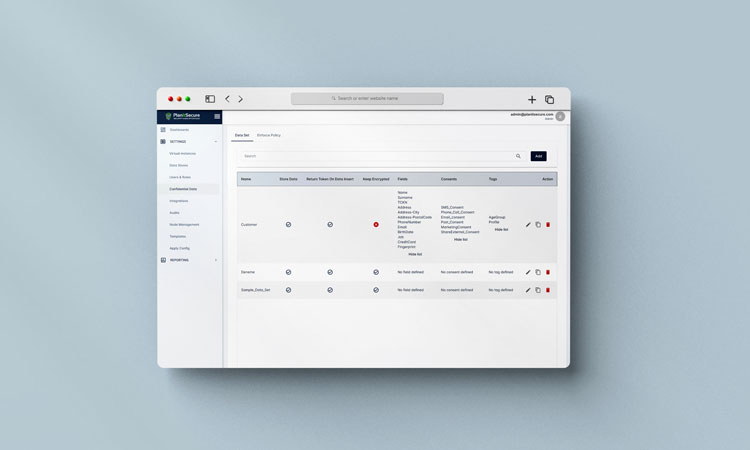
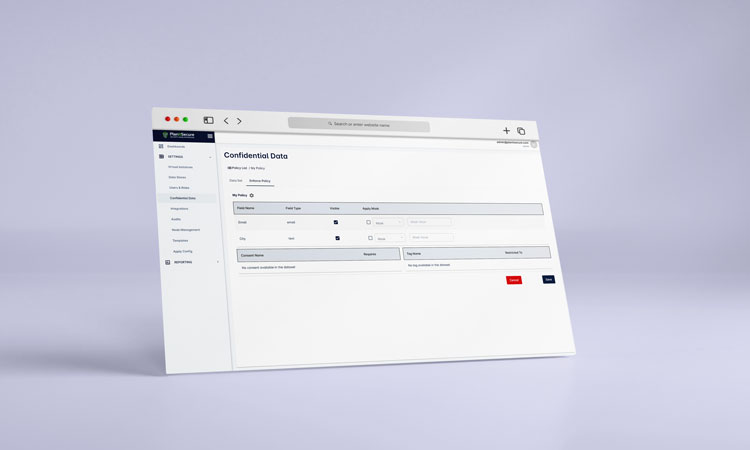
Consent management for building transparency and trust
Consent management helps you build trust with your customers by empowering them to determine what personal data they want to share with you and for what purposes. Access to customer data must always be in accordance with customer consents.
Customers are concerned about their personal data more than ever before. Consent management solves this problem by empowering customers in letting them determine what personal data they want to share with an organization and for what purposes.
You can configure different types of consents, such as communication channel (sms, email, phone call), purpose (service, marketing) for each person that your organization collects personal information from. Consents helps to ensure application users/roles can access that personal data for legitimate business purposes only, and in accordance with regulations. For example, a marketer can see the records of individuals that gave marketing consent, but not others; email address is only exposed if email consent has been given by the customer.
PlanItSecure also enables you to take auto actions when consent states changes. For example, you can configure it to automatically pseudonymize the email address field when email consent is revoked or send a notification to the admin when marketing consent expires.
Tokenization for secure data sharing with other applications
Enable developers to easily and freely share customer data without concern for data security and data theft
Tokenization is the process of turning a meaningful piece of data, such as an individual’s record, into a random sequence of characters called a token that has no meaningful value if breached. Since there is no way to extract the original data from a token, apps can freely share tokens (confidential data) with other apps without concern for whether it will be stolen.
When real data needs to be retrieved, the token must be submitted to PlanItSecure ,and after the successful authorization process and access controls, real data will be fetched and delivered.
Independent logs for audit and regulatory compliance
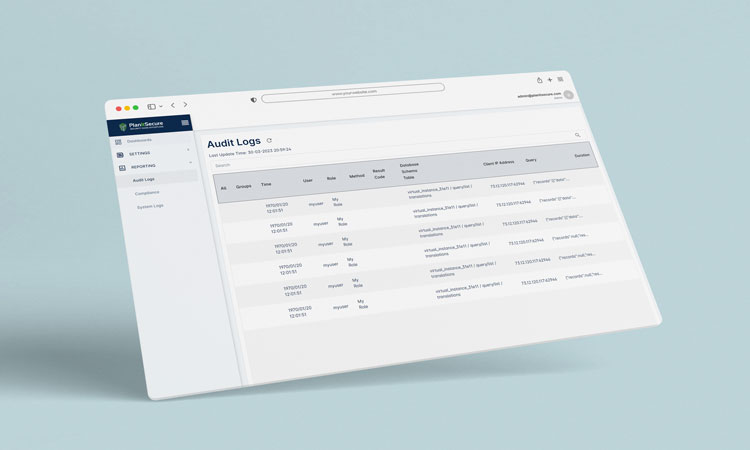
PlanItSecure tracks and monitors all administrative configuration changes and data access activities on confidential/personal data and stores them as independent logs for internal audit, forensic activities, and regulatory compliance.
Want to understand how PlanItSecure made
GDPR compliance effortless for developers ?

Email: contact@planitsecure.com
Address :
260 Madison Avenue
New York, NY 10016
Teknopark Istanbul
Sanayi Mahallesi Teknopark Bulvari
Bina:1/4C No:213
34906 Pendik/Istanbul
copyright 2023 PlanItSecure

